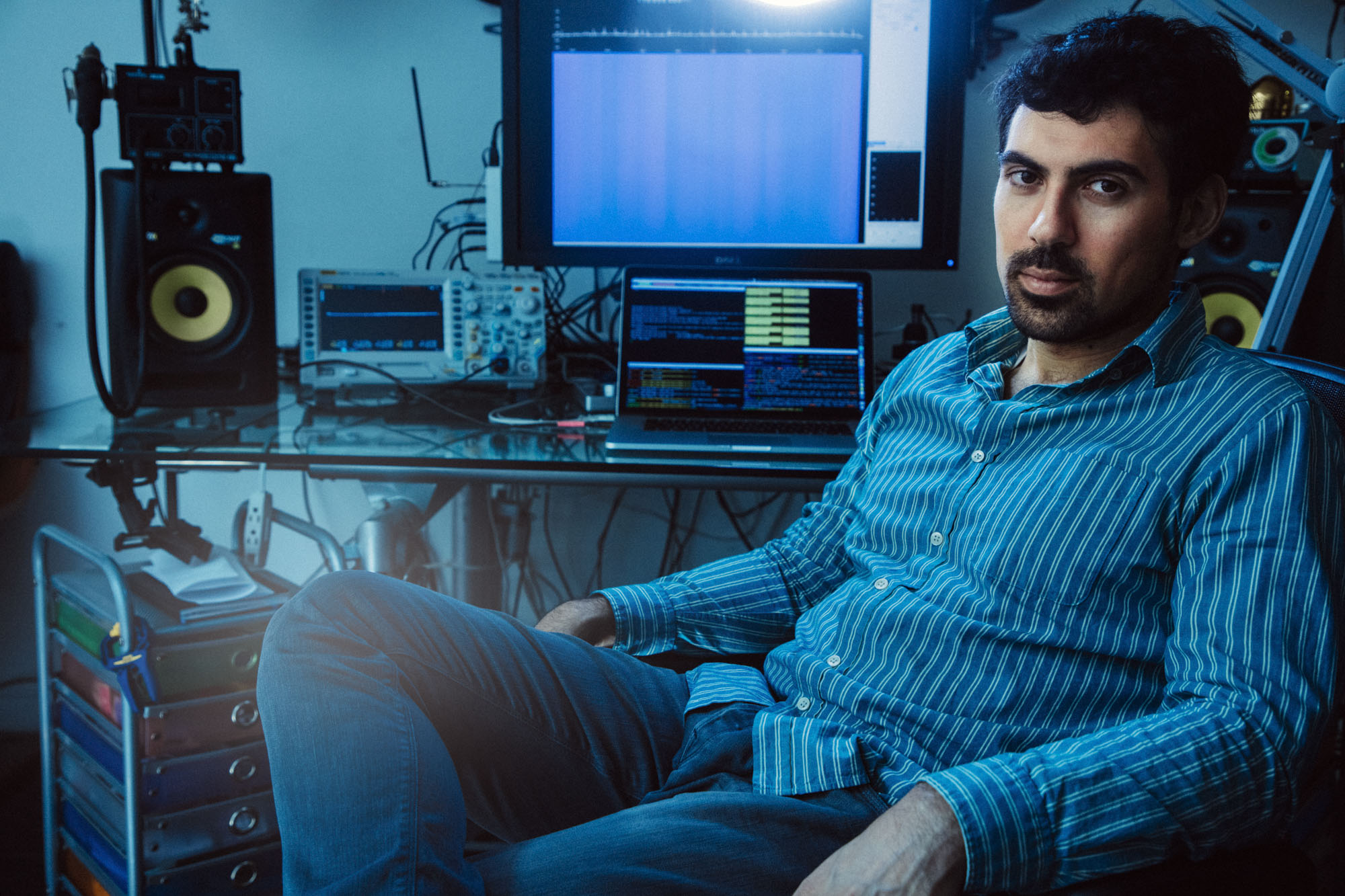
Samy Kamkar is a famous "grey hat" hacker. That means he's not bad, but he's not quite good either. A high school drop out, he gained attention (and a felony charge) for his 2005 "Samy worm" virus on MySpace, which added "Samy is my hero" to victims' profiles. Since then, he actually has become something of hero, with hacks that publically demonstrate—often to the chagrin of corporations and the US government—security weaknesses and vulnerabilities. (When Amazon announced they would use drones, he figured out how to hack one and posted the video on his YouTube channel.) He also isn’t afraid to play whistleblower, as he proved in 2011 with headline-making research on how Google and Apple surreptitiously collect user data. Below, we talk with Samy about computer-jumping viruses, government cyber warfare and a fun little hack you can try at home.
Ok so, first thing’s first, what is the biggest risk to our personal data right now?
When it comes to technology, if you’re trying to exploit something, you’re looking for the weakest link and we, as humans, are the weakest link. I think passwords are a terrible thing. We are inherently bad at remembering them so we use either short weak ones or the same ones across multiple sites.
Smart TVs, cell phones, cars—everything is internet-connected now so there are ways to get in. But most hackers aren’t going to go to that effort if they can get to you more easily through password theft. If it’s a criminal organization doing it, they probably aren’t even targeting you personally. They just want to make money.
How can we better protect ourselves?
One, use a password manager like 1Password, there are a couple out there, I don’t have a specific preference. They make really hard passwords to use. And I suggest that you use one that protects all of your passwords with a single password. That way, you will only have to remember one password and it will do the rest for you. It will log in to websites and if any of the individual ones get hacked, only that password has been hacked and nothing else.
Second, use two-factor authentication. It’s basically an extra level of security that links something you know (like a password) with something you have (like a phone or email address). So when you go to sign in to a website it might send a login to your phone that you then have to enter.
Of course, for you, password theft is child’s play. You deal more in the sophisticated exploitation of technology.
Yes, how technology works and how we can break in, because there are governments and criminal organizations—lots of groups—using those techniques. They aren’t just going for a little bit of money with ransomware and passwords. They’re more far-reaching attacks that are targeting, let’s say, political figures or entire nation states. The Stuxnet virus is an example. No one has ever admitted creating it but the consensus is that the US and Israeli governments worked together to create this virus that spread across the internet to attack Iranian nuclear reactors and essentially shut them down. But here’s where it gets crazy: the nuclear reactors weren’t even on the internet. So why send a virus when you can’t even reach them?
The Stuxnet virus was targeted to the laptops of specific Iranian contractors. And once it got into their laptops, it was specially crafted to jump from the computer into any USB drive that they plugged in. So one of the contractors goes to upgrade software on one of the nuclear reactors; they take the infected USB out of their computer and log into the reactor and the virus jumps off of the USB drive into the nuclear reactor and actually shuts it down. That’s crazy to be able to create something that can jump from machine to USB drive to nuclear reactor! So if that happened five or ten year ago, imagine what governments have created since then.
So when you see these headlines declaring cyber terrorism as the next big threat to world order, you agree? They’re not doomsday-ing for the sake of clicks?
While headlines may be overblown today, the threat is becoming more likely as more industrial systems like power plants, nuclear facilities, and other services have their systems connected to the internet, or connected to other networked systems. Like even electricity and water, those are controlled by data systems that someone could hack into and wreak havoc on cities.
Do you have a nightmare scenario?
Electromagnetic pulses can be crazy because they actually destroy electronics. It requires a lot of power and they’re kind of localized but someone could just come near your house and destroy all your electronics. People taking electric grids down would also be bad, traffic light systems—there are just a lot of unfortunate situations that I hope don’t happen.